 Title: A Bug Hunter’s Diary. A Guided Tour Through the Wilds of Software Security.
Title: A Bug Hunter’s Diary. A Guided Tour Through the Wilds of Software Security.
Author: Tobias Klein
ISBN: 978-1-59327-385-9
Published: November 2011
Websites: http://nostarch.com/bughunter.htm, http://www.trapkit.de/books/bhd/en.html
In the modern times of noisy news headlines like “A Security Researchers Unveils a Critical Vulnerability in Product X”, little is publicly said about the overall bug hunting process, in lieu of discussions regarding technical bug details, exploitation mitigations and their countermeasures. The taste of identifying a target, finding a vulnerability, creating proof-of-concept code and talking to the vendors was only known to those actively participating in the security scene – but only until Tobias Klein published his book called A Bug Hunter’s Diary. Mr. Klein, a German security researcher, decided to let the reader take a glimpse at how a bug hunter’s daily work looks and feels like; a subject as much interesting as underestimated in the common literature.
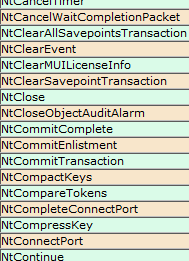
The book is divided into eight chapters and a brief Appendix. The Introduction outlines basic concepts, assumptions and tools used by the author and commonly referenced thorough the book. After that follow seven technical chapters, each discussing a vulnerability in a different product, found and responsibly disclosed by the author during the course three years (2008 – 2011). The diversity of software classes discussed in the book ranges from media decoders (VLC, FFmpeg) through web browsers (WebEx ActiveX control) up to kernels and device drivers (Solaris, Mac OSX, Apple iOS, Avast! driver). Thanks to the wide selection of presented hardware and software platforms and products, one can learn how all kinds of software can be subject to fundamentally trivial bugs, and how different vendors have completely different policies and response times in regard to external reports.
What I consider the biggest advantage of the book is the specific layout of the chapters. Each of them is arranged in the form of a story, beginning with an initial concept of how to approach a chosen target and ending with a patch release and advisory publication. This goes far beyond the typical scheme of limiting focus to technical aspects of software security only, and makes the book enjoyable for anyone interested in vulnerability discovery.
As a diary, I believe it is one of the best books I have read so far. Easy writing style, interesting bugs and illustrative pictures and code listings are the key points making it so successful. Bear in mind, though, that it should not be confused with a textbook – if you are looking for a complete overview of common vulnerability classes or information regarding exploitation mitigations such as DEP or ASLR, you’d rather refer to The Shellcoder’s Handbook or a similar volume. That said, I would especially recommend A Bug Hunter’s Diary as an excellent supplement of a security textbook to everyone making his first steps in the software security field. I definitely wish to see more books of this kind published in the future.
 Friday, the 7th of September 2012 we were supposed to play the securitytraps.no-ip.org CTF. Unfortunately, the competition was postponed for a later date at the last moment, due to some significant technical problems. Next day evening we accidentally discovered another CTF taking place – the nullcon 2012 CTF, which sadly had already started one day earlier. Nonetheless, there were still 24 hours until the end, so we decided to give it a shot. TL;DR: We ended up 3rd (Team 41414141).
Friday, the 7th of September 2012 we were supposed to play the securitytraps.no-ip.org CTF. Unfortunately, the competition was postponed for a later date at the last moment, due to some significant technical problems. Next day evening we accidentally discovered another CTF taking place – the nullcon 2012 CTF, which sadly had already started one day earlier. Nonetheless, there were still 24 hours until the end, so we decided to give it a shot. TL;DR: We ended up 3rd (Team 41414141).
 Every one or two quarters, there’s the one day we all wait for – and that’s when the latest issue of the Hack in the Box Magazine is released :-) Thanks to the hard and awesome work of
Every one or two quarters, there’s the one day we all wait for – and that’s when the latest issue of the Hack in the Box Magazine is released :-) Thanks to the hard and awesome work of 
 Five weeks ago, we have taken part in a fancy game-development competition aka Google GameJam 48h. As the name implies, the contest lasted for precisely two days; unfortunately, we were proven to lack supernatural powers and had to spend some of the precious time sleeping :-) The theme of the event was “Magic versus Science”, and in our case, those two days of hardcore coding resulted in a 2D logic game called
Five weeks ago, we have taken part in a fancy game-development competition aka Google GameJam 48h. As the name implies, the contest lasted for precisely two days; unfortunately, we were proven to lack supernatural powers and had to spend some of the precious time sleeping :-) The theme of the event was “Magic versus Science”, and in our case, those two days of hardcore coding resulted in a 2D logic game called